- CALL: 877-560-4261
- LIVE DEMO
- LOG IN
-
Healthcare Compliance & HIPAA Articles

Do Not Click “Later”: Why Healthcare Patch Policies Matter Before the Update Becomes Urgent
A practical HIPAA Security reminder for busy healthcare teams: patches protect systems, but policies and procedures make protection reliable...
View Details »
Malware Has Terrible Manners: How One Quiet Threat Can Disrupt a Healthcare Organization
Malware has terrible manners. It does not knock. It does not introduce itself. It does not politely announce, “Hello, I am here to disrupt your systems and create a compliance headache.” It shows up pretending to be...
View Details »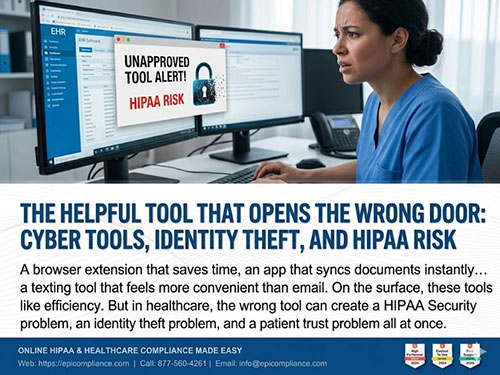
The Helpful Tool That Opens the Wrong Door: Cyber Tools, Identity Theft, and HIPAA Risk
Every healthcare organization wants to work faster. That is just reality. Teams want easier scheduling, smoother messaging, quicker file sharing, better remote access, and fewer steps between a task and its completion. That is...
View Details »
THE DIGITAL FRONT DOOR: WHY CYBERSECURITY IS A DAILY HABIT, NOT AN IT TASK
Picture this: Midway through a hectic afternoon at a family clinic, a nurse glances at her overflowing inbox while hurriedly wrapping up patient notes. Her phone buzzes nearby. Just as she reaches for her next task, an alert...
View Details »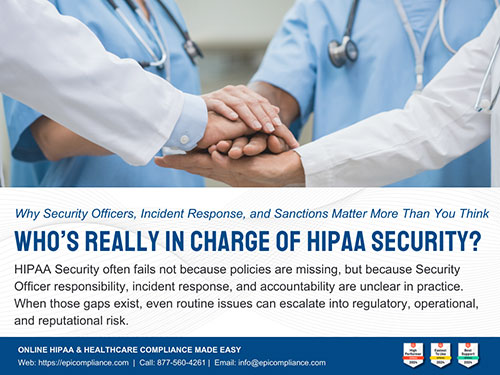
Who’s in Charge of HIPAA Security? | Security Officer, Incident Response & Sanctions
In many healthcare organizations, HIPAA Security lives in a gray zone. IT assumes compliance owns it. Compliance assumes IT has it covered. Leadership trusts that policies alone are enough. Then a staff member clicks...
View Details »
New Year, New Shield: Why Your Risk Assessment is the Heartbeat of Your Practice
It’s January. In the healthcare world, this usually means a flurry of new insurance cards, updated patient forms, and the inevitable "New Year, New Me" energy. But while everyone else is focused on resolutions, a savvy...
View Details »
Security Incidents: Not Every Incident is a Breach, But Every Incident Counts
Ransomware, phishing, stolen laptops, and cloud mix-ups have basically become background noise in healthcare. In 2023, we saw a record number of attacks—averaging almost two breaches a day...
View Details »
Accounting of Disclosures – Can You Show Who Saw What?
If a patient walked into your practice today and asked, “Who outside your organization has seen my record in the last six years?”, could you answer with confidence and documentation, not guesswork...
View Details »
Password Protection: Your First Line of Defense
In the world of healthcare compliance, every password is more than a key — it’s a safeguard for patient privacy. Passwords protect access to your email, electronic health records (EHR), billing platforms, and internal...
View Details »
How prepared is your team for HIPAA’s 2025 Security Rule changes?
When most people think about protecting patient records, they imagine locked cabinets and restricted office areas. But in healthcare today, sensitive information rarely stays in one place. It travels with staff on laptops, it’s stored on...
View Details »
Beyond Encryption: The Overlooked Habits That Make or Break Security
When most people hear “HIPAA Security,” they picture high-tech hackers typing furiously in a dark room. But here’s the truth: the biggest risks often come from the everyday habits we don’t think twice about...
View Details »
Don’t Fall for the Workstation Trap: How One Unlocked Screen Can Sink Your Compliance—and What You Can Do About It
Let’s be real: when you think of a data breach, you probably picture hackers in hoodies, furiously typing away in a dark basement. But the truth is, many breaches start with something way more ordinary—like a computer left unlocked...
View Details »
Is Your Front Door the Biggest Threat to Your Digital Life?
We're all programmed to fear the faceless hacker in a dark room, miles away, plotting to steal our data. But what if the most significant risk isn't a brilliant piece of code, but a simple unlocked door? In the world of...
View Details »
HIPAA Security and Business Associates: What You Need to Know in 2025
In today’s healthcare landscape, the security of patient data extends far beyond the walls of your clinic or hospital. The Health Insurance Portability and Accountability Act (HIPAA) requires not only covered entities...
View Details »
Cybersecurity Essentials: Patches and Policy Awareness
Remember back in 2017 when headlines screamed about the WannaCry ransomware attack? It wasn't just a distant tech problem; it brought parts of critical systems, like the UK’s National Health Service, to a grinding...
View Details »
When the Digital Becomes Dangerous: Understanding the Threat of Malware
It's a strange thought, isn't it? We buy baby monitors for peace of mind, wanting to keep a watchful eye on our little ones. Yet, there are unsettling stories—real cases—where hackers have wormed their way into...
View Details »
Combating Identity Theft in Healthcare: A Critical Responsibility
Healthcare organizations are the guardians of some of the most sensitive personal information: medical records, Social Security numbers, insurance details, and more. Imagine the devastating consequences...
View Details »
Cyber Tools: Your Secret Weapon for HIPAA Compliance
In today’s digital healthcare landscape, things can get a bit dicey. Imagine a cozy clinic suddenly facing a ransomware attack that locks them out of patient records for days. Not only did they have to pay...
View Details »
Cybersecurity & HIPAA: Protecting Patient Data from Digital Threats
We all have tons to do and very little time to do it. So when an extra security step like Multi-Factor Authentication (MFA) pops up, it doesn’t exactly make our day better—or move us any faster. We groan when...
View Details »
The HIPAA Security Officer: A Crucial Role in Protecting Patient Data
Let’s face it—cyber threats are everywhere, and healthcare organizations are prime targets. From ransomware attacks to data breaches, the risks to sensitive patient information are growing every day. That’s why having a...
View Details »
Securing Healthcare Data: Strategies to Protect e-PHI and Achieve Compliance
Have you ever wondered how your healthcare provider keeps your sensitive information secure? Protecting patient data isn’t just about compliance with regulations—it’s about maintaining trust, ensuring privacy, and delivering quality care. For...
View Details »
Understanding Accounting of Disclosures and Security Incidents Under HIPAA: What You Need to Know
When it comes to HIPAA compliance, few topics are more crucial—or more misunderstood—than Accounting of Disclosures and Security Incidents. These two areas lie at the heart of patient privacy and data security, affecting covered entities like doctors...
View Details »
Protecting Patient Data: A Deeper Look into Password Security and HIPAA Compliance
In healthcare, securing sensitive patient data isn’t just a responsibility; it’s a legal requirement under HIPAA (Health Insurance Portability and Accountability Act). With the increase in cyber threats targeting healthcare, a fundamental aspect...
View Details »
HIPAA and Encryption: Fortifying Patient Data in the Digital Age
In the healthcare sector, protecting patient privacy is just as important as delivering quality medical care. As electronic health records (EHRs) and other digital tools become the norm, healthcare organizations must prioritize data protection. One of...
View Details »
Understanding Access Controls Under HIPAA: What Every Healthcare Worker Needs to Know
In today’s healthcare environment, protecting patient information isn’t just a responsibility—it’s a legal obligation. Whether you’re a medical assistant, nurse, doctor, dentist, front desk staff member, billing clerk, transcriptionist, or security...
View Details »
Fortifying HIPAA Compliance through Robust Physical and Workstation Security
Safeguarding patient information has never been more critical in an era of increasingly sophisticated data breaches and cyber threats. The healthcare sector, which relies heavily on electronic protected health information (ePHI), must adhere...
View Details »
Strengthening the Security Chain: The Critical Role of Business Associates and BAAs in HIPAA Compliance
The healthcare ecosystem thrives on collaboration, but when it comes to safeguarding patient privacy, the stakes are high. The Health Insurance Portability and Accountability Act (HIPAA) establishes a comprehensive framework to protect...
View Details »
Securing Healthcare Systems: The Crucial Role of System Patches in HIPAA Compliance
Maintaining the integrity and security of patient information is paramount in the healthcare sector. Ensuring your systems are up-to-date with the latest patches is a vital aspect of HIPAA compliance and overall data security. This article...
View Details »
HIPAA Policies and Procedures: A Guide for Healthcare Organizations
The Health Insurance Portability and Accountability Act (HIPAA) safeguards patients' Protected Health Information (PHI). For healthcare organizations, adhering to HIPAA is both a legal requirement and an ethical obligation. This article dives...
View Details »
Malware Mayhem in Healthcare: Protecting Patient Privacy in the Digital Age
The healthcare industry thrives on sensitive information. Patient records brim with personal details, diagnoses, treatment plans – a treasure trove for malicious actors in the digital world. Malware, a catch-all term for malicious software...
View Details »
Identity Theft in Healthcare: Mechanisms, Impacts, and Preventative Strategies
Identity theft in healthcare not only compromises the financial stability of individuals but also poses a significant threat to the privacy and security of patient information, directly impacting healthcare providers' compliance...
View Details »
Harnessing Cybersecurity Tools for Enhanced HIPAA Compliance
In late February 2024, Change Healthcare, a unit of UnitedHealth Group (UHG), fell victim to a cybersecurity incident. The attack disrupted healthcare operations across the country, affecting hospitals, doctors, pharmacies...
View Details »
From Desktops to Smartphones: Building a Multi-Layered Defense Against Cyberattacks, Mobile Vulnerabilities, & Email/Texting Risks
As a dedicated healthcare professional, you're likely accustomed to using mobile devices and email for patient communication, as well as for interaction with colleagues and business associates. While adhering to data security best practices...
View Details »
Avoid Audits and Fines: Building a Proactive HIPAA Strategy with Security Officers, Incident Response, and Sanction Policy
If you work in the healthcare industry, you know how important it is to protect the privacy and security of your patient's health information. You also know how challenging it can be to comply with the Health Insurance Portability...
View Details »
Unveiling Accounting of Disclosures: A Crucial Element of HIPAA Compliance
If you are a healthcare provider, a business associate, or a patient, you may have heard of the term "accounting of disclosures" in relation to HIPAA. But what does it mean, and why is it important for HIPAA compliance? In this article, we will explain...
View Details »
Password Protection: How to Create and Remember Strong Passwords
Do you use passwords like "123456", "iloveyou", or your pet's name? If so, you are putting your online accounts and personal information at risk. Hackers can easily guess or crack these passwords and access your data...
View Details »
Reinvigorating Trust: A Fresh Perspective on Encryption & HIPAA Security
Let’s address the elephant in the room: articles on encryption, cybersecurity, and HIPAA compliance are abundant, often leading to a saturation of information. However, revisiting these topics with a fresh lens is critical as it directly impacts the...
View Details »
The HIPAA High-Wire: Balancing Patient Privacy with Access Controls
Ever felt that heart skip when you can't locate your phone in your bag or pocket? That surge of panic? It's just a fraction of what medical professionals feel when they sense a hint of vulnerability in patient data security. For our indispensable...
View Details »
Achieving HIPAA Compliance Made Easy: A Step-by-Step Guide
Maintaining HIPAA compliance is crucial for any organization dealing with protected health information (PHI). However, navigating the complex requirements of the Health Insurance Portability and Accountability Act (HIPAA) can be a daunting task...
View Details »
How to Protect Yourself After the HCA Healthcare Data Breach
Imagine waking up one morning to a flurry of alerts and warnings— your data has been compromised. If you are one of the 11 million patients potentially impacted by the recent HCA Healthcare data breach, you don't have to imagine...
View Details »
Safeguarding Health: HIPAA, Physical Security, and Workstation Protection
"If privacy is boiling hot... HIPAA is the fire underneath," observes Mac McMillan, a seasoned health IT leader, and CEO of CynergisTek, a top cybersecurity consulting firm. Healthcare professionals and business associates like IT professionals...
View Details »
OCR's Strong Authentication Guide for HIPAA Compliance
Robust authentication measures enhance the security of electronic protected health information (ePHI), reduce the risk of unauthorized access or breaches, and demonstrate compliance with HIPAA's requirements for safeguarding patient information...
View Details »
HIPAA Mistakes and Misconceptions: Guide for Foreign-Educated Healthcare Workers
Healthcare workers in the United States must navigate the complexities of Protected Health Information (PHI) and the Health Insurance Portability and Accountability Act (HIPAA). This is especially true for healthcare workers who may not yet...
View Details »
Columbus Children's Hospital Exposed Employees to Workplace Violence
Columbus Children's Hospital in Ohio is under scrutiny following a recent investigation conducted by the US Department of Labor. The investigation revealed that the hospital failed to safeguard its employees, including nurses...
View Details »
Defending Patient Privacy: The Power of System Patches and HIPAA Security Policies
System patches are like digital shields that enhance security and optimize performance. They fix vulnerabilities and protect against evolving cyber threats...
View Details »
Streamline Healthcare Compliance - Top Easy-to-Use Solution and Review
Healthcare compliance is crucial to the smooth operations of healthcare organizations, and it is essential to comply with all relevant laws and regulations to avoid legal issues and maintain...
View Details »
5 Main Reasons for HIPAA Violations and Fines
Here are the top 5 reasons for HIPAA fines and violations that every Covered Entity and Business Associate should know:
View Details »
OSU-CHS Hit with $875K Penalty for HIPAA Violations: A Wake-Up Call for Healthcare Providers
Healthcare professionals, HIPAA Covered Entities, and Business Associates are all tasked with protecting the sensitive health information of patients. The recent $875,000 penalty imposed on OSU-CHS for HIPAA violations should serve as a wake-up call...
View Details »
5 Main Reasons for Medicare Violations and Fines
While Medicare is designed to ensure access to affordable healthcare, healthcare providers must adhere to strict guidelines to avoid violations and fines.
View Details »
Password Protection
Digitalization acceleration. With the advent of modernization and technology, we see digitalization as a valuable and convenient method of doing transactions in our daily life. For instance...
View Details »
Malware
As the need and dependency of people and businesses on computers, mobile gadgets, electronic data, and a variety of programs and applications consistently...
View Details »
How Encryption plays an important role in HIPAA Security
The University of Rochester Medical Center (URMC) has paid a $3 million HIPAA penalty to the Office for Civil Rights (OCR) of the U.S. Department of Health and Human Services...
View Details »
Security Incidents and Sanction Policy
• Forgotten to remove access of a departing employee?
• Forgotten to collect devices with potential PHI from departing employees?...

ID Theft and ID Protection
On March 23, 2021, acting United States Attorney M. Rhett DeHart announced that according to the Federal Bureau of Investigation’s 2020 Internet Crime Report, South Carolinians lost more than...
View Details »
Embracing HIPAA Security at Home and at Work
We certainly live in interesting times. I mean, my mother that is 87 years old, received a tablet for her Christmas present. My three-year-old grandson uses his mother's cell phone...
View Details »
Do you have a Business Associate Agreement with your vendors?
Business Associates
In an ideal world, each healthcare provider (aka Covered Entity) has a...

Password Management in HIPAA Compliance
Does HIPAA mention anything about passwords?
Yes. Password and Password Management are explicitly stipulated in the following provisions:
First, under "Definitions" [45 CFR 164.304] of the "Security...

Access Controls
§ 164.312(a)(1)
Allow access to ePHI only to those granted access rights. Implementation specifications under Access Control...

What is Accounting of Disclosures?
Also known as Accounting of Disclosures of Protected Health Information, it is a mandate under 45 CFR § 164.528 of the Security and Privacy, Subpart E - Privacy of Individually Identifiable Health Information...
View Details »
CISA and AHA issue urgent warnings: CYBERTHREAT on US Healthcare Organizations
With the current critical and dangerous events unfolding, there is no avoiding discussion of unsettling threats – particularly cyber threats...
View Details »
IN A GLANCE: HIPAA Security Officer, Security Incidents, and Sanction Policy
Q: Is a HIPAA Security Officer necessary? Can we make do without having one? A: The short answer is "No."...
View Details »
Open Notes as Mandated by the 21st Century Cures Act: A Clinician's Condensed Guide
In 2016, the 21st Century Cures Act came into effect under President Obama; as of April 5th, 2021, the program rule on...
View Details »
HIPAA Physical Safeguards and Workstation Security
Physical Safeguards (45 CFR § 164.304) refers to physical measures, policies, and procedures to protect a covered entity’s or business...
View Details »
Do Business Associates have direct liability under HIPAA?
The U.S. Department of Health and Human Services (HHS), Office for Civil Rights (OCR), issued a fact sheet enumerating a list of HIPAA...
View Details »
Is Encryption Essential in HIPAA Compliance?
“Encryption is a method of converting an original message of regular text into encoded text. The text is encrypted by means of an algorithm...
View Details »
System Patch Management Role in HIPAA Security
By this time you should have a basic understanding of cybersecurity, cyber attacks, cyber tools, and malware. If you need a refresher on these...
View Details »
The Flexibility of Approach Clause on HIPAA Policies and Procedures
The words "policies" and "procedure(s)" are not specifically defined in HIPAA. However, in the publication...
View Details »
Know what HIPAA says: Security Officer, Security Incidents, and Sanction Policy
Assigning a HIPAA Security Officer is one of the mandates of HIPAA as indicated in 45 CFR § 164.308 (a) (2). It specifically...
View Details »
Aetna to pay $1 million in fines plus Corrective Action Plan for HIPAA breaches according to OCR HHS findings
Aetna has entered into a resolution agreement with the Office of the Civil Rights (OCR), U.S. Department of Health and Human Services...
View Details »You worry about your business. Let us take care of compliance. To learn more about HIPAA Healthcare Compliance and how we can help, please call:
877-560-4261 or contact us at any time.